JavaScript async generators
 Did you know that you can combine
await
with
generators
in a JavaScript for loop? The
for await … of
construction is very handy in this ES6-Promise-everywhere-JavaScript
world. In this post, we'll go through a simple example consuming data from
a paginated API like GitHub.
Did you know that you can combine
await
with
generators
in a JavaScript for loop? The
for await … of
construction is very handy in this ES6-Promise-everywhere-JavaScript
world. In this post, we'll go through a simple example consuming data from
a paginated API like GitHub.
Happy 2018
Finally found some time to write something, it's been a while. Programming (and blogging) on my free time has been relegated to the background theses months, partly because I'm busy playing hide-and-seek and also because I've become fond of painting and drawing (by the way I highly recommend drawabox). Still, here are the few things I've been exploring.
I completed the 2017 edition of Advent of Code in Swift and it was a blast. I picked Swift because I wanted to learn something new (also "mobile" is a thing now — or so I've read on the internet). It was easy to setup and run on Linux and has what you would expect of a "modern" programming language (clean syntax, optionals, package manager etc.). The killing feature though is the custom operators allowing you to define new operators including their associativity, precedence, and using fun Unicode characters. Compared to Rust I feel like Swift has a much, much smoother learning curve. On the other hand, learning Swift has not changed the way I see programming the way learning Rust has. You can find my puzzles and solutions here.
I started Crafting Interpreters because of how fun it is to write compilers. And the book is incredible. It's a pure engineered labour of love. I can't imagine how many hours of dedicated work it has been (and continue to be) for its author, Bob Nystrom. I plan to use Swift and Rust instead of Java and C, you can take a look at my attempt here.
Finally, I recently discovered the cryptopals crypto challenges (also known as The Matasano Crypto Challenges). Write "real" crypto code then break real crypto code, what's not to love about it? Not for the faint of heart, but definitely an enlightening journey. Code at GitHub as usual.
That's it for now, happy coding :)
Implementing MD5 in AWK

It is only recently that I've discovered the Advent of Code, a coding challenge happening on December (though available all year) since 2015 and it is quite unique. I've set out to solve the 2015 puzzles in AWK (you can find my solutions here). Very soon one of them required to compute (a lot of) MD5 hashes. After some research, I found out there are basically three solutions:
- Using a pipe. This is expected to be slow, relying on an external program, but very simple to implement.
- Write a dynamic extension in C or C++. This should yield very good performances, but would be limited to GNU Awk and tedious to deploy as it would require compiling.
- Implement MD5 in AWK. This is expected to be portable and very slow, but more importantly a lot of fun.
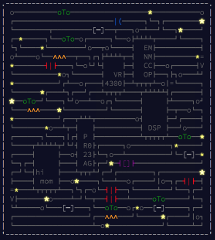
In this post I'll go through the implementation of MD5 in AWK by first writing a GNU Awk version (because of some of its features), then porting to AWK, and finally optimizing. The main challenge is that MD5 is basically a lot of bitwise operations on 32-bits integers and AWK has neither. If that sounds interesting to you, sit comfortably and read on — this is going to be a long ride.
OpenBSD daily(8) on Linux
Not long ago, I had to setup an Ubuntu VM (I'm running them through
bhyve by the way, and it's really
sweet). But the day after, to my surprise, the lovely heartbeat email
$hostname daily run output I've been used to was nowhere to be
found. After a quick check, the Ubuntu cron "periodic" stuff doesn't
output anything unless something go wrong.
I could easily add scripts into the
/etc/cron.daily directory, but then I would
have to handle the output "by hand" if they should or should not report
something and the email subject would be the ugly cron line:
Cron <root@$hostname> test -x /usr/sbin/anacron || ( cd / && run-parts --report /etc/cron.daily )
Ultimately I realized that my dream was something like OpenBSD daily(8) that I am used to (they say old habits die hard). Since they are simple POSIX shell scripts, I've hacked them a bit to run on Ubuntu.
Strong crypt scheme with Dovecot, Postfixadmin and Roundcube

Hi everyone, happy new year :)
While Dovecot support a lot of different password schemes, making both Postfixadmin and Roundcube playing nice by using something else than the old MD5 scheme need a little work.
In this post I'll explain how to configure them to use a Blowfish scheme (BLF-CRYPT in the Dovecot terminology), but you can easily adapt the steps to use something else. You should already have Dovecot, Postfixadmin, and Roundcube (with the password plugin) up and running.
Dovecot antispam with Rspamd (part 2)
Ahoy !
I realized that forgot about half of the
Rspamd &
Dovecot in
my last article,
so here is an attempt to correct this misstep.
In this article we'll configure Dovecot's
Sieve to understand how Rspamd assign spam
score and headers to emails. Then, we'll implement policies to reject
or filter spam from Sieve. If needed, we'll use the
spamtest and spamtestplus Sieve extensions.